
Enhancing Cloud Security Governance Strategies With Google Cloud Platform
Identity and access governance on Google Cloud
A clear identity and access governance model on Google Cloud may begin with mapping organizational roles to cloud identities and defining a lifecycle for those identities. Common elements include role separation between administrative and operational functions, use of service accounts for machine identities, and mechanisms for granting temporary or scoped access. Organizations often track access via audit logs and may use automated processes to revoke stale privileges. Identity governance typically seeks to balance operational needs with the principle of least privilege while keeping auditability and reversibility in view.
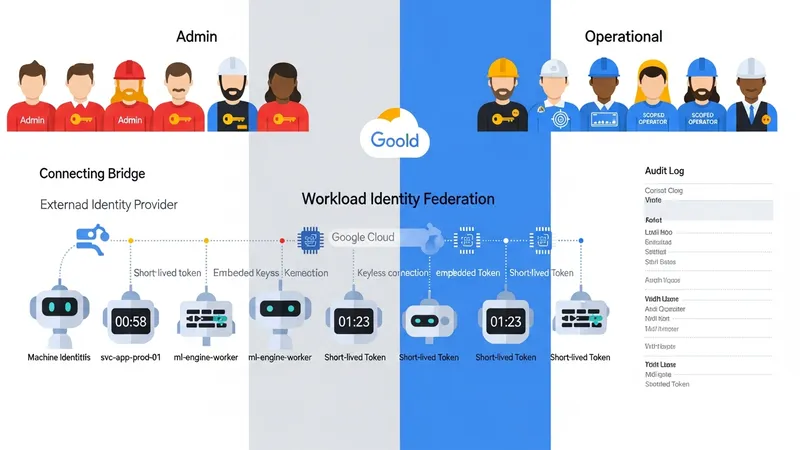
Service accounts and workload identities can be managed to reduce long-lived credentials and to enable fine-grained permissions for automated workflows. Patterns that are often employed include unique service accounts per workload, use of short-lived tokens, and constrained scopes for permissions. Workload identity federation or comparable approaches may be used to avoid embedding static credentials in code or artifacts. These measures commonly reduce the window of exposure if credentials are compromised and support more predictable access control.
Role design is a practical consideration; predefined roles, primitive roles, and custom roles each present trade-offs. Predefined roles may map to common cloud functions, while custom roles allow organizations to tailor privileges more closely to business tasks. Governance programs commonly include processes for creating and approving custom roles, documenting intended use, and periodically reviewing role assignments. Role assignment patterns may also be combined with groups or external identity providers to streamline administration at scale.
Operational considerations include automating access reviews, enabling detailed audit logging, and integrating identity events with alerting and ticketing systems. Periodic certification processes and emergency access procedures are often documented so that governance teams can respond to incidents while maintaining traceability. These considerations may be expressed in policy documents and supported by tooling that enforces and reports on access-related requirements.