
Enhancing Cloud Security Governance Strategies With Google Cloud Platform
Network and perimeter control strategies for Google Cloud
Network governance frequently focuses on establishing segmentation and minimizing public exposure of services. Typical constructs include virtual private clouds with subnetting, network firewalls, and route controls that together define traffic boundaries. Organizations may adopt patterns for isolating environments such as development, staging, and production, and for restricting cross-project traffic. These patterns often combine with identity controls to ensure that network-level protections complement access policies rather than replace them.
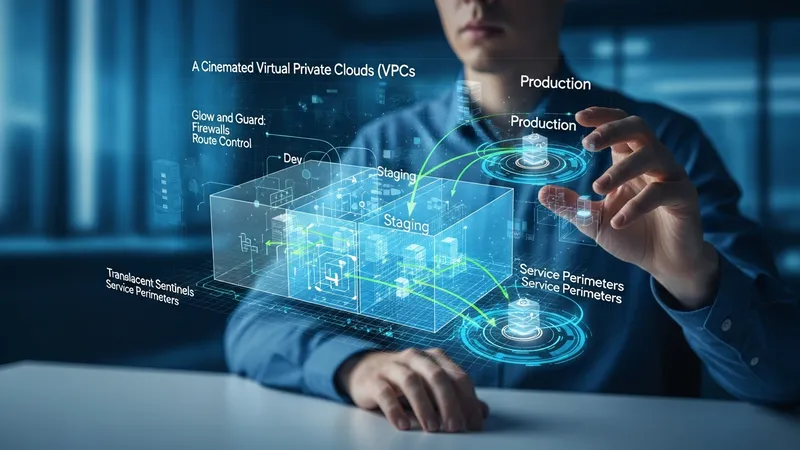
Perimeter controls may be implemented to constrain data egress and to limit access to managed services. Examples of control patterns include service perimeters or private connectivity mechanisms that restrict interactions between projects or external networks. Such perimeters commonly aim to reduce unintended data exfiltration and to enforce regulatory or internal constraints on where data may be accessed. Perimeter design is often influenced by application architecture and data classification policies.
Firewall rules, routing policies, and load-balancing configurations are operational elements that may be governed through standardized templates and automated deployment pipelines. Infrastructure as code approaches can be used to version network configurations and to run pre-deployment checks against policy constraints. Governance frameworks may specify acceptable default rules, required exceptions processes, and test procedures to validate that network segmentation meets stated objectives.
Testing and validation are typical governance activities for network controls. Organizations may schedule regular vulnerability scans, configuration audits, and segmentation tests to confirm the effectiveness of perimeter defenses. Findings from these activities often feed back into governance cycles to refine policies and to update templates or constraints. This feedback loop helps maintain alignment between architectural changes and governance expectations.